
From Detection to Correction: The Missing Layer in Enterprise Security
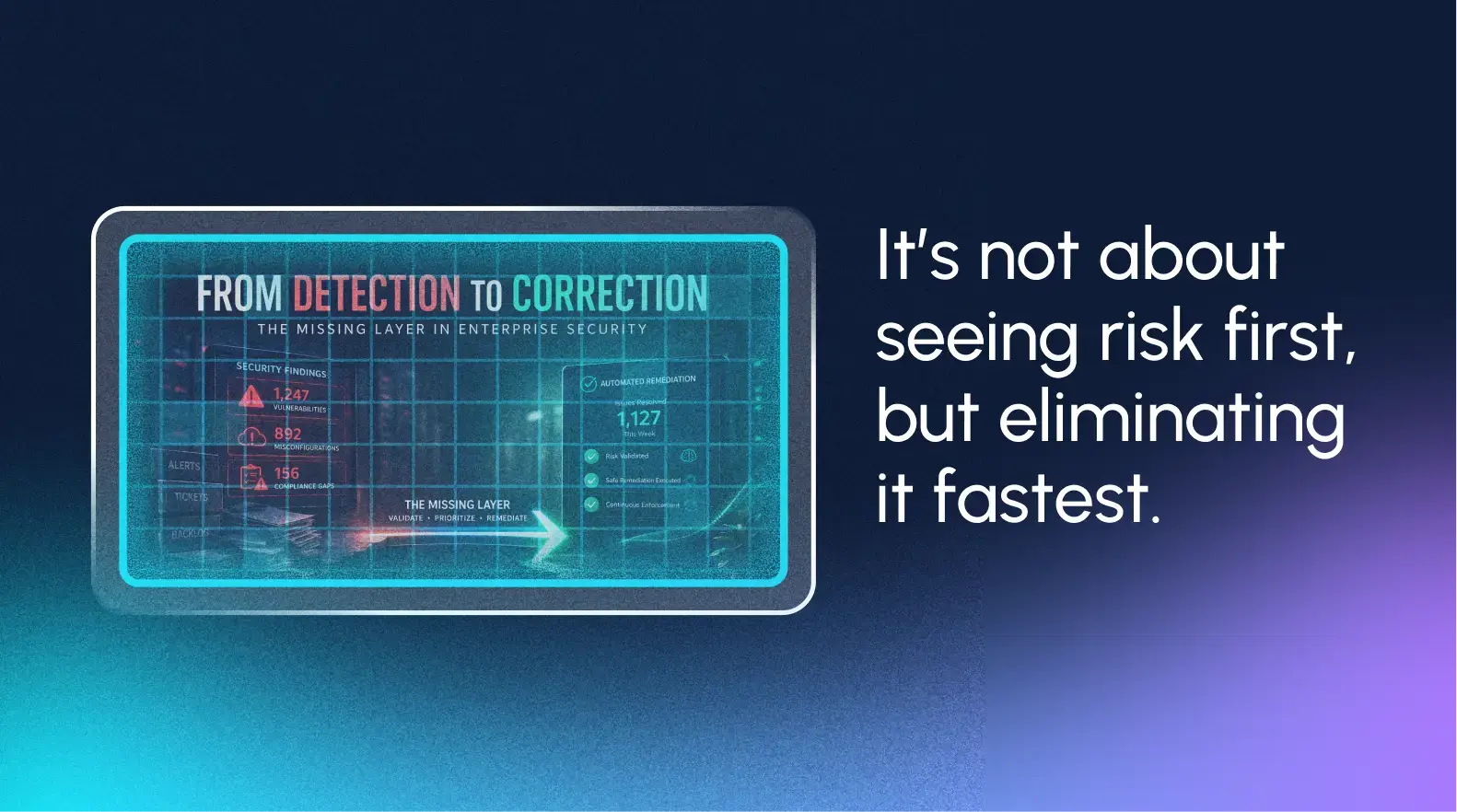
Every CISO knows the feeling. Your security tools complete their latest round of scans. The dashboards light up. Hundreds - sometimes thousands - of vulnerabilities, misconfigurations, and compliance gaps surface across your environment.Everything is visible.
And yet, six months later, many of those same issues remain unresolved.
This is the paradox of modern enterprise security. Organizations have become exceptionally good at finding problems, but they still struggle to fix them.
The Industry Has Mastered Detection - But That’s No Longer Enough
For the past decade, the industry has invested heavily in detection technologies. Vulnerability scanners, EDR platforms, SIEM systems, cloud security tools - all designed to answer one question:
What is wrong with my environment?
Today, most enterprises can answer that question with precision.
But a more important question remains unanswered:
How quickly can you fix what’s wrong?
This isn’t just an operational challenge. It reflects a broader industry shift.
In its 2026 research on preemptive cybersecurity, (Gartner ID: G00847391),1 Gartner® concludes that traditional, reactive security approaches are becoming obsolete in the face of AI-driven threats and expanding attack surfaces. Organizations must move toward anticipating and neutralizing risk before it materializes.
In other words, the problem is no longer visibility. The problem is action.
Drowning in Alerts, Starving for Remediation
Modern security teams operate in an environment of overwhelming visibility.
A typical enterprise deploys multiple tools across vulnerability management, endpoint protection, cloud security, and compliance. Each produces a steady stream of findings, alerts, and recommendations. The result is a complete, continuously updated picture of risk.
Security teams know exactly what is wrong. But knowing is not fixing.
Take a common example. A vulnerability scanner identifies a deprecated protocol enabled across thousands of devices. The risk is clear. The recommendation is straightforward.
Then reality sets in.
-
Which systems actually depend on it?
-
What breaks if it is disabled?
-
Who owns those systems?
-
What is the rollback plan?
-
When can changes be safely deployed?
What begins as a simple finding turns into a multi-week or multi-month remediation effort.
Multiply that across hundreds or thousands of issues, and the backlog becomes inevitable.
Reliance on reactive indicators - signals that only appear after an attack has begun - forces organizations into a constant state of catch-up. And attackers exploit that gap.
They do not need zero-days when known vulnerabilities remain unaddressed for weeks or months.
The Detection-Correction Gap Is the Real Risk
The gap between detection and correction is not just inefficient. It is dangerous.
When remediation takes 30, 60, or 90 days, organizations are effectively providing attackers with both a roadmap and a timeline.
Industry data shows that the majority of successful attacks exploit known, preventable issues. Misconfigurations, outdated protocols, unpatched systems - all detected, but not corrected in time.
The business impact is significant:
- Security teams spend hours triaging and ticketing
- Infrastructure teams are pulled into reactive remediation cycles
- Compliance efforts stall due to unresolved findings
- Risk accumulates despite full visibility
Perhaps most critically, organizations develop a false sense of security.
Visibility creates confidence. But without action, that confidence is misplaced. What’s missing is not another detection tool. It's the layer between detection and correction.
Detection tells you where you are vulnerable. Correction is what actually reduces your attack surface.
The Missing Layer: From Visibility to Action
For years, the model has been:
detect → prioritize → ticket → wait
That model no longer works at machine speed.

What’s emerging in its place is a new paradigm:
detect → validate → remediate → enforce
This is the shift toward preemptive exposure management - where systems do not just identify risk, but actively validate and neutralize it, often with minimal human intervention.
For example, instead of flagging a risky configuration and creating a ticket, the system can immediately determine that the problematic protocol has not been used in 90 days, validate that remediation is safe, and fix it instantly across thousands of devices.
To get there, organizations need capabilities that traditional tools do not provide:
Contextual Understanding
Know not just what is misconfigured, but whether it matters - usage, dependencies, and business impact.
Cross-Environment Execution
Apply the right fix across operating systems, cloud platforms, and device types automatically.
Safe Rollback
Make every change reversible to eliminate the fear of breaking production systems.
Continuous Enforcement
Ensure issues stay fixed by automatically correcting configuration drift.
From Reactive Security to Preemptive Outcomes
Forward-thinking organizations are beginning to close this gap. Rather than treating remediation as a manual, ticket-driven process, they are adopting approaches that integrate validation and correction directly into the security workflow.
Platforms like Remedio enable this shift by allowing teams to move directly from detection to safe, automated remediation, reducing large portions of their attack surface in minutes instead of months.
Low-risk issues can be resolved instantly. Higher-risk scenarios are enriched with context, allowing teams to make faster, more informed decisions.
It's little wonder, then, than Gartner® sees exposure management evolving beyond visibility into autonomous interdiction - where systems validate and mitigate risk in real time.
The results are significant:
- Remediation cycles shrink from months to minutes
- Backlogs are reduced dramatically
- Security teams shift from reactive to proactive
- Attack surface is continuously minimized
Early adopters of these capabilities are not just detecting threats faster. They are neutralizing them before they can be exploited.
The Path Forward: Fix-First Security
The future of enterprise security is not about better detection. It is about closing the loop between detection and correction.
Closing that gap requires a shift in mindset:
From measuring success by vulnerabilities detected, to measuring success by vulnerabilities remediated.
From periodic remediation cycles, to continuous risk reduction.
From reactive workflows, to proactive posture management.
Organizations that move to adopt preemptive cybersecurity capabilities will be able to neutralize risks proactively, rather than reacting after damage occurs.
Remedio was built to deliver exactly that - enabling organizations to safely and scalably remediate the issues, known or unknown, that would quietly persist for fear of downstream impact, complicated coordination, or lack of resources.
Because in modern security, the goal is no longer to find everything. It is to act on exposure before attackers do.
- Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
- GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
_____
- Gartner, Emerging Tech: Top Solution Capabilities in Preemptive Cybersecurity, 1 April 2026
About Author

Mor Bikovsky
Subscribe to
our Newsletter
We are ready to help you until and unless you find the right ladder to success.
Related Posts
Join over 25,000 in beating the failure of strategies by following our blog.
Modern cybersecurity faces a strange paradox: the stronger organizations make th...
8 minute read
Leading cybersecurity today often feels like navigating without coordinates. Tea...
6 minute read
IT, or Information Technology, is responsible for managing an organization’s tec...
6 minute read
Device posture refers to the security health and configuration state of an endpo...






Comments