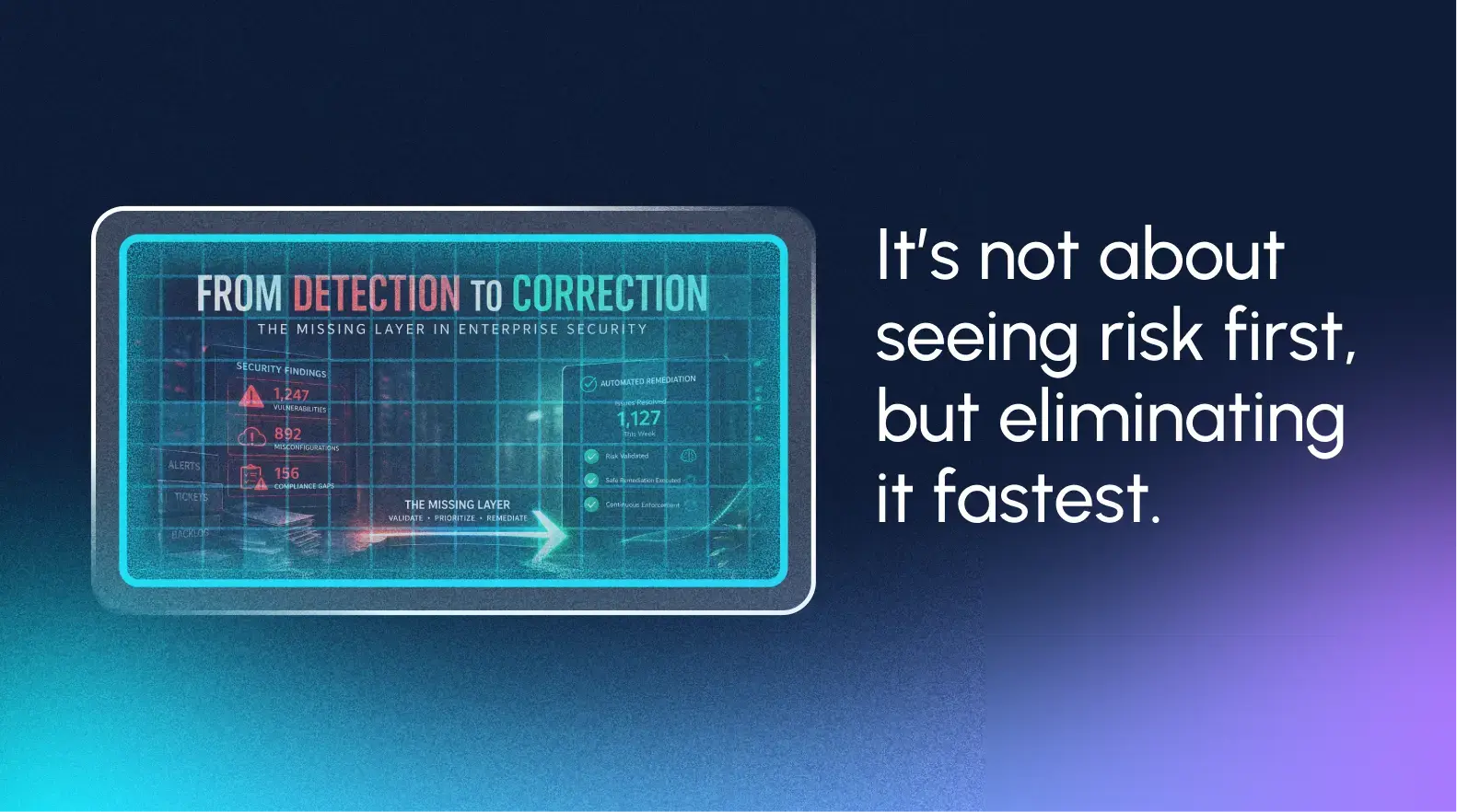
Beyond Alerts: How Remedio Helps Eliminate Exposure (And Fast)
Just how much damage can one misconfiguration cause? At PDS Health, the answer was stark: a single misconfiguration threatened 4,600 PCs and disrupted daily operations.
Beyond Alerts: How Remedio Helps Eliminate Exposure (And Fast)
Just how much damage can one misconfiguration cause? At PDS Health, the answer was stark: a single misconfiguration threatened 4,600 PCs and disrupted daily operations.